▶ Previous Review
In the last SASE popular science, we emphasized that the core value of SASE lies not in "function superposition" but in "architecture reconstruction". Through the deep integration of network and security, zero-trust access control, and cloud-native architecture, SASE transforms enterprise security from static perimeters to dynamic protection, and shifts access control from trusting networks to trusting identities.
As the third article in the series, this issue focuses on three typical application scenarios of SASE in actual enterprise environments. It analyzes how SASE achieves the integrated capability of "efficient connectivity + dynamic security" under different network architectures and business requirements.

1. Secure Networking for Multi-Branch Enterprises: Achieving Intelligent Scheduling of Global Interconnection
Enterprises supporting global businesses in industries such as manufacturing, retail, and logistics often have multiple cross-regional branches or data centers requiring interconnection. Traditional security solutions deploy security devices at the network perimeters of data centers and office locations, imposing high requirements on enterprise investment and operation and maintenance. These solutions cannot adapt to the cloud migration trend—security risks intensify and network flexibility bottlenecks become prominent once businesses expand or system data migrates to the cloud.
Solution Logic
SASE adopts SD-WAN intelligent wide-area network as the underlying architecture, combined with global POP points to achieve nearby access and link acceleration, ensuring low latency and high availability of cross-regional communications. On the security front, SASE edge nodes integrate components such as Firewall as a Service (FWaaS), Intrusion Prevention System (IPS), and Web Application Firewall (WAF), enabling security policies to take effect immediately at the transmission edge with defense capabilities "flowing with traffic". Enterprises can achieve visualized network topology, centralized policy delivery, abnormal traffic detection, and security log auditing through a unified cloud-based console, realizing an intelligent secure networking experience of "global visibility and unified orchestration".
2. Remote Mobile and Hybrid Work Scenarios: Bidding Farewell to the Traditional VPN Era
With the expansion of business scales, remote mobile and hybrid work have become the new normal for modern enterprises. These scenarios often involve access requirements to internal applications or networks from multiple identities, including internal/outsource employees, supply chain partners, and customers, using various terminals such as mobile phones, tablets, and PCs. Although traditional VPN solutions provide unified account remote access, they are unsuitable for such scenarios and cannot adapt to the cloud application trend (especially with multiple public clouds). Additionally, the underlying "excessive trust" flaw in VPN architecture poses risks—account password leaks increase the threat of data exposure attacks.
Solution Logic
SASE introduces a zero-trust architecture to reconstruct access logic: traditional VPN clients are replaced with SDP (Software-Defined Perimeter) clients, and VPN gateways are replaced with SDP gateways to close internet exposure surfaces. It enables unified cloud-based Identity and Access Management (IAM) and Multi-Factor Authentication (MFA), establishing secure encrypted transmission channels only after verifying multiple identity factors including user, device, network, time, and location. During access, Secure Web Gateway (SWG) and behavior analysis engines continuously detect traffic patterns and abnormal behaviors, immediately blocking suspicious sessions. Enterprises can achieve full-cycle security control at the user, device, and session levels. Regardless of identity or location, users can enjoy a seamless experience of "anytime access, on-demand authorization, and secure connectivity".

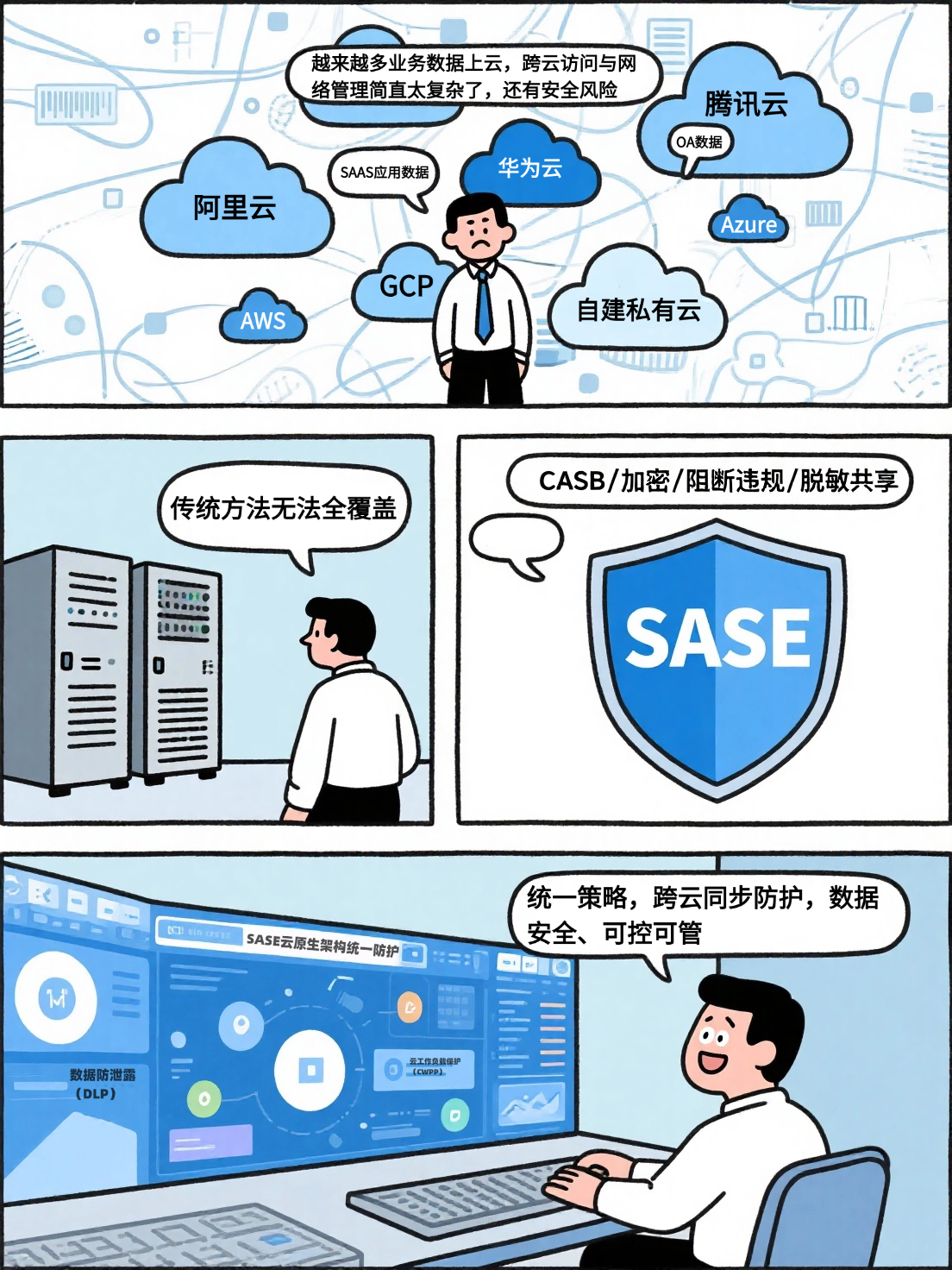
3. SaaS Access and Hybrid Cloud Scenarios: Providing "Secure Passports" for Cloud Data
With the deepening of digitalization, enterprise IT architectures are gradually becoming cloud-based, internet-based, and mobile. For organizations with highly decentralized businesses and multiple branches, enterprise data and SaaS applications are often distributed across different public clouds, private clouds, and hybrid clouds. Multi-cloud architectures integrated with SaaS applications have become mainstream, complicating cross-cloud access and network management. This shifts the traditional data center-centric network security architecture to a multi-center model focusing on cloud, branches, and mobile users, blurring network security perimeters and posing significant security challenges.
Solution Logic
SASE implements enterprise-level security policies around cloud resources through Cloud Access Security Broker (CASB), achieving unified supervision of various cloud-based SaaS platforms. Positioned between users and cloud service providers, CASB provides in-depth visibility and granular control—such as automatic encryption of sensitive files, real-time blocking of non-compliant uploads, and dynamic sharing of desensitized data—to help enterprises better manage cloud access and protect cloud data. Meanwhile, SASE's cloud-native security policy engine can synchronously execute unified protection rules across public and private clouds. Combined with Data Loss Prevention (DLP) and Cloud Workload Protection Platform (CWPP) policies, it ensures data remains "traceable, controllable, and manageable" across multi-cloud and hybrid cloud environments.
✅ Summary: SASE Architecture Becomes a Must-Have for Digital Enterprises
The value of SASE lies in enabling digital enterprises to truly achieve "secure access to all resources anytime, anywhere" amid the trends of globalization, internetization, cloudification, and mobility. It reduces the burden on network IT administrators, improves efficiency, and transforms security from a "post-event patch" to a "security gene embedded in enterprise network connectivity". SASE is evolving from a conceptual framework to a mandatory requirement for digital security in future global enterprises.
I can help you refine a **SASE typical application scenarios comparison table** to clearly present the differences between traditional solutions and SASE solutions in each scenario. Would you like me to create it?





